MySQL in the Cloud: Oracle Cloud Infrastructure Leads the Way
The move to the cloud is no longer a trend; it’s a necessity. Businesses, especially those seeking to modernize their IT environments, are ... Read More
Learn more about why Eclipsys has been named the 2023 Best Workplaces in Technology and Ontario, Certified as a Great Place to Work in Canada and named Canada’s Top SME Employer!
Learn more!Did you know, Cloud computing is the fastest-growing technological innovation in the business world? Organizations across all different industries are in a tech race and continue to embed the cloud at the core of their operations. Several essential factors need to be leveraged correctly and taken into consideration when maximizing your ROI in the cloud. One is the concept of Cloud Security. As a business, you do not want all the remarkable benefits of the cloud undermined by a failure to maintain strong cloud security practices. As organizations transition from an inelastic on-premise estate to flexible cloud-enabled solutions, it is critical that all cloud deployments are integrated with existing security policies/architecture. The difficulty lies in the strategy it takes to get there, which is ultimately a team effort between vendor and enterprise.
Many may argue that “Cybersecurity” and “Cloud computing” are two topics that contradict. One requires you to store data off-site, trusting a vendor to keep your data/transactions safe and the other requires building a virtual security network around your data. The reality is that these two traditionally distant practices develop a synergistic relationship out of necessity for users. The product of this relationship is Cloud Security. Cloud-based applications must be shielded from attack, and data in the cloud must be protected against unauthorized access. With Cloud architecture being much different than architecture on-prem, organizations must look beyond traditional security tools and approaches to their protect data & transactions.
Some things for organizations to take into consideration about Security in the Cloud:
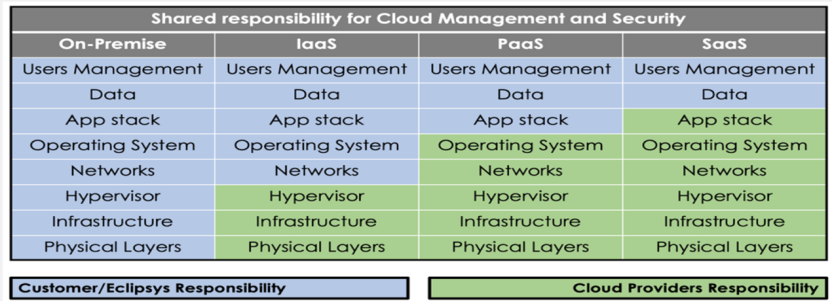
Understanding your role in security is paramount to ensuring your data will not be compromised. Your responsibility will depend on your cloud deployment model (public, private, multi-cloud, etc.). Engaging with Eclipsys can help you manage those areas that continue to be your responsibility.
Ultimately, IT organizations can stay on top of cloud security by staying informed, ensuring you or your staff are adequately trained and continuing to operate with a healthy level of caution (compliance and auditing). These are the teams best positioned to optimize their investment in the cloud. Eclipsys Solutions has just recently been designated as the only Certified Oracle Cloud Solutions Provider in Canada. This recognizes our solutions architects as having the deployment experience and technical expertise needed to manage and secure both Oracle and non-Oracle workloads in the cloud. Ask our experts about your team’s journey to the cloud.
The move to the cloud is no longer a trend; it’s a necessity. Businesses, especially those seeking to modernize their IT environments, are ... Read More
The move to the cloud is no longer a trend; it’s a necessity. Businesses, especially those seeking to modernize their IT environments, are ... Read More